What Is IT Infrastructure Outsourcing & What Are Its Benefits?

Concerns about hidden costs, slow response times, or reduced oversight often give IT infrastructure outsourcing an undeserved bad name. In practice, the benefits of IT infrastructure outsourcing include stronger system stability, lower capital outlay, and consistent protection for servers, storage, networks, and cloud platforms.
| “An experienced partner should extend your capabilities, not limit them. The right provider helps you achieve stability, security, and efficiency.” – Peter Bertran, Chief Client Officer, DKBinnovative |
Outsourcing infrastructure moves routine maintenance, monitoring, and upgrades out of your internal workload and into a structured service model. This approach cuts the risk of sudden hardware expenses, speeds recovery from outages, and gives businesses access to advanced tools that are costly to maintain in-house.
This article will define IT infrastructure outsourcing, explain how it differs from general IT outsourcing, and outline the steps that help organizations effectively capture these advantages.
What is IT Infrastructure Outsourcing?
IT infrastructure outsourcing is when an organization partners with an external provider to manage core technology systems such as servers, storage, networks, and cloud platforms. Instead of maintaining and upgrading this environment in-house, businesses rely on specialized teams who provide monitoring, maintenance, scaling, and security.
How is IT Infrastructure Outsourcing Different Than General IT Outsourcing?
While IT infrastructure outsourcing can be part of an IT outsourcing contract, it isn’t always in all cases. The key difference between the two is as follows.
| General IT Outsourcing | IT Infrastructure Outsourcing |
| Covers a broad range of functions, including IT helpdesk support, application management, and cybersecurity. | Focuses specifically on the foundation of technology, including IT networks, servers, data centers, storage, and cloud platforms. |
The Top Benefits of IT Infrastructure Outsourcing
Reduced Downtime
Downtime affects productivity, revenue, and customer trust. Infrastructure outsourcing provides 24/7 monitoring and proactive maintenance, which keeps servers and networks performing consistently. The result is fewer interruptions and faster recovery when problems occur.
Predictable Costs
Infrastructure ownership comes with unpredictable expenses such as emergency repairs or sudden hardware replacements. With outsourcing, these expenses become part of a stable monthly agreement. This model simplifies budgeting and reduces financial risk tied to infrastructure upkeep; it’s the top reason why 70% of companies that outsource do so.
Faster Recovery
When outages occur, outsourced providers use specialized monitoring platforms and automation tools to identify and resolve issues quickly. This reduces downtime compared to in-house teams that may lack dedicated staff for rapid response. Faster recovery helps businesses maintain continuity and protect operations from extended interruptions.
Stronger Security
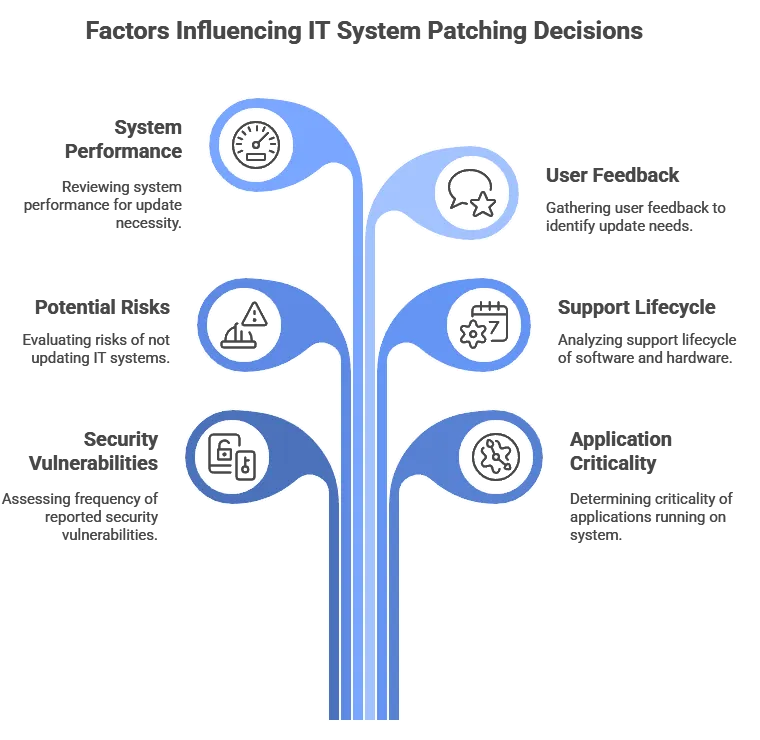
Infrastructure-level security requires constant vigilance and expertise. Providers manage patching, network firewalls, and intrusion detection systems to close gaps that attackers target. By outsourcing, businesses gain access to security practices that are difficult and expensive to build internally.
This can have additional tangential business benefits since 48% of consumers say that they would not purchase from a company if they had cybersecurity concerns about their practices.
Find Out How We Maintain 98.39% Client Satisfaction |
Lower Capital Outlay
Purchasing servers, storage, and networking gear requires significant upfront spending. Infrastructure outsourcing removes this burden by delivering these resources as a service. That’s because moving away from on-prem solutions has an average 2.3x lower total cost of ownership. Businesses can redirect capital toward growth initiatives while still benefiting from enterprise-grade infrastructure.
Enterprise-Grade Tools
Providers invest in advanced monitoring, automation, and reporting systems to manage client infrastructure effectively. These platforms deliver insights and proactive alerts that many organizations cannot afford to maintain on their own. By outsourcing, companies gain the benefits of these tools without direct ownership costs.
Improved Resilience
Outsourced infrastructure often includes disaster recovery planning, backup management, and redundancy. These measures reduce the risk of extended outages caused by hardware failure or unexpected events. Improved resilience means businesses can maintain operations even when disruptions occur.
| Take a Closer Look at What Else You Can Get From an IT Partner |
How to Approach IT Infrastructure Outsourcing
1. Assess Your Environment
The first step is to document your existing infrastructure, including servers, storage, and networks. This assessment should identify costs, recurring issues, and areas where performance does not meet expectations. A clear baseline helps determine which functions are best suited for outsourcing.
2. Set Clear Goals
Outsourcing works best when objectives are defined in advance. Goals may include reducing downtime, improving compliance, or lowering infrastructure spending. Clear targets make it easier to evaluate provider performance and measure success after implementation.
3. Choose Carefully
Not all providers specialize in infrastructure. Selecting a partner with demonstrated expertise in servers, cloud platforms, and networking is critical. Reviewing certifications, client references, and service history ensures the provider can deliver reliable infrastructure support.

4. Transition of Infrastructure Control
You shift operational control of infrastructure systems (servers, storage, networks, cloud environments) from your internal team to the provider. This includes handing over monitoring tools, access credentials, configuration management, and system baselines. The provider takes over applying patches, upgrades, capacity planning, and infrastructure health monitoring consistent with the SLAs.
5. Integration & Validation
Once control is transferred, the provider integrates with your existing systems and tools (identity systems, virtual machines, storage arrays, etc.). They validate performance, security, and redundancy in the new setup. You run tests, failover drills, and performance benchmarks to confirm the infrastructure meets agreed standards before fully switching over.
| Find Places to Outsource Your IT Infrastructure in The State of Texas | ||
| Irving | Plano | Frisco |
Outsource Your IT Infrastructure With DKBinnovative
Handing over your infrastructure is a big decision. The wrong provider can leave you with hidden costs, slow response times, and security gaps. Choosing a partner with the right expertise protects your business and reduces those risks.
DKBinnovative specializes in managing critical infrastructure, including servers, networks, storage, and cloud environments. Our team provides 24/7 monitoring, proactive maintenance, and security controls that keep systems stable and compliant.
Contact us today to get started.